Welcome Avatar!
The DeFi landscape consists of familiar financial products such as borrowing and lending, trading exchanges, and investing strategies in fully digital form.
Traditional intermediaries like banks and brokerages are replaced by automatic software code.
DeFi code is open source, allowing anyone to study and improve it
DeFi transactions are relayed to peer-to-peer blockchain networks, allowing anyone to participate
The promise is a global and permissionless financial system.
But. DeFi users face a number of security challenges
hacks (computers, ‘phones, wallet software, DeFi websites)
smart contract vulnerabilities (bugs that allow hackers to drain virtual banks)
financial scams (creativity of scammers is endless!)
Smart investors who are willing to do thorough research can invest with a degree of safety and reap the financial rewards. We created DeFi Education to help you.
Today, we’re going to provide insights on how to use DeFi safely, drawing on our experience in software security and as DeFi power users for several years.
Why Security Matters
Transactions are irreversible once confirmed on the blockchain. This means if a fraudulent transaction is entered, the funds are lost forever.
Recourse to the legacy legal system is unlikely to result in recovery of funds, especially as some of the most prominent hackers have ties to the governments of unfriendly states. Ironically, your best chance is if a “white hat hacker” rescues the funds.
The safety of your DeFi funds is largely influenced by your education and discipline.
It’s essential to take appropriate security measures to ensure:
only you have access to the private keys which control your funds; and
you are educated about the products you use (avoid scams)
Key Takeaway: DeFi is only as secure as your behaviors
Self Custody
“Your Keys, Your Bitcoin. Not Your Keys, Not Your Bitcoin.”
A simple rule, but what are the “keys” in this famous quote?
Private keys, the component of the public-private cryptography system which makes blockchains like Bitcoin and Ethereum work. A private key is a secret number which is mathematically linked to the public address (derived from the public key) which can hold crypto assets.
All movement of funds in crypto involves the holder of the private keys for an account address broadcasting a *signed* message instructing the blockchain to move funds to another account. A valid signature requires possession of the private key.
Private keys are designed to be unforgeable, so unless an attacker knows your private key he cannot send a valid transaction which moves funds out of your custody.
A private key is just a long number. But humans aren’t good at memorizing numbers.
A seed phrase is a useful invention which encodes a number as a set of 12-24 easily memorizable words. If you know the words, software can ‘derive’ a whole set of private keys and their corresponding public addresses.
This means that you can recover access to all of your crypto accounts at any time, from anywhere in the world by remembering 12 words! There’s no better way to move money across borders which doesn’t force you to give up custody.
Seed phrases are the access code to your money and should be kept secret at all times.
Some investors make durable physical backups of their seed phrases, engraving them on fireproof metal plates. And there are complex multi-signature schemes available to ensure that funds can be moved only if a minimum number of trusted parties sign the transaction. Multi-sig signing is suitable for estate planning, corporate use, and for individuals with significant crypto holdings.
Third Party Custody
There are legitimate institutional grade third party custody providers who carry insurance, use cold storage, and have audited procedures. They’re not suitable for most investors due to high account minimums. Certain custodians are probably safe.
But. Most “retail” investors custody their crypto with companies who would not stand up to any rigorous due diligence. Most of these cowboy firms likely invest the customer money, use it for their operations, or otherwise expose customers to risks.
This may or may not be disclosed frankly in the Terms and Conditions.
When BlockFi filed bankruptcy last year, DeFi Education subscribers weren’t surprised. We’d already done a deep dive on the deceptive marketing behind the BlockFi Interest Accounts which led to record fines by US regulators. Shockingly, the company was allowed to continue operating *and* people kept depositing funds.
“BlockFi never had enough collateral to fully back all the loans made” DeFi Ed, Feb 15 2022
Crypto companies who want your deposit have a well oiled marketing machine. You might have even seen expensive adverts (even stadium naming rights) and heard about their political contributions and charity work.
But you can’t see their books in real time!
One of DeFi’s greatest advantages is that you can see the reserves of any protocol and know in real time whether it is able to meet obligations. Even better, smart contracts can be designed so the protocol cannot continue to incur liabilities while insolvent.
This isn’t the case when you trust third party custody.
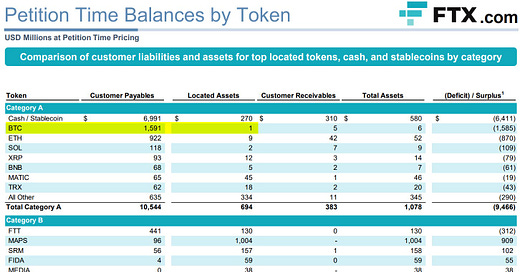
Customers deposited nearly $1.6 billion of Bitcoin with crypto exchange FTX. After filing for bankruptcy, only $1 million worth of Bitcoin could be located.
Who controls the “missing” Bitcoin now? We’ll probably never know.
Key Takeaway: self-custody is the best solution for most who can study how to do it correctly
Hardware Wallets
A cryptocurrency “wallet” is a piece of software or hardware which has two functions
store your private key (seed phrase)
sign crypto transactions
If you only used a software wallet - a program on your computer or phone (example: MetaMask) then the private key (seed phrase) is stored on your device. This means if your device is hacked, the attacker can steal all your crypto!
A hardware wallet is a self-contained device which generates and stores your private keys. You need to plug into your computer or link with your mobile device to make transactions. Unless you approve the transaction on your hardware wallet, the funds won’t be moved.
A hardware wallet doesn’t protect you against being tricked to sign a transaction. You still need to learn and follow good security practices.
Offline Signing
Offline signing is a security technique that involves creating and signing cryptocurrency transactions on an offline device, such as an airgapped PC wallet, and then broadcasting the transaction to the blockchain using an online device.
Like a hardware wallet, offline signing greatly reduces the risk that your private keys can be stolen by a hacker as they are never entered on an Internet-connected device.
You can learn how to perform offline signing for Bitcoin and Ethereum transactions in this *free* article
DeFi App Security
DeFi is powered by Smart Contracts: self-executing computer programs that run on the blockchain and are designed to execute transactions automatically when conditions are met.
An example of a condition could be: only allow the user to withdraw all his deposited collateral when his loan has been repaid in full. A bug in implementing these conditions could allow a borrower to take a loan, withdraw collateral, and never repay his debt.
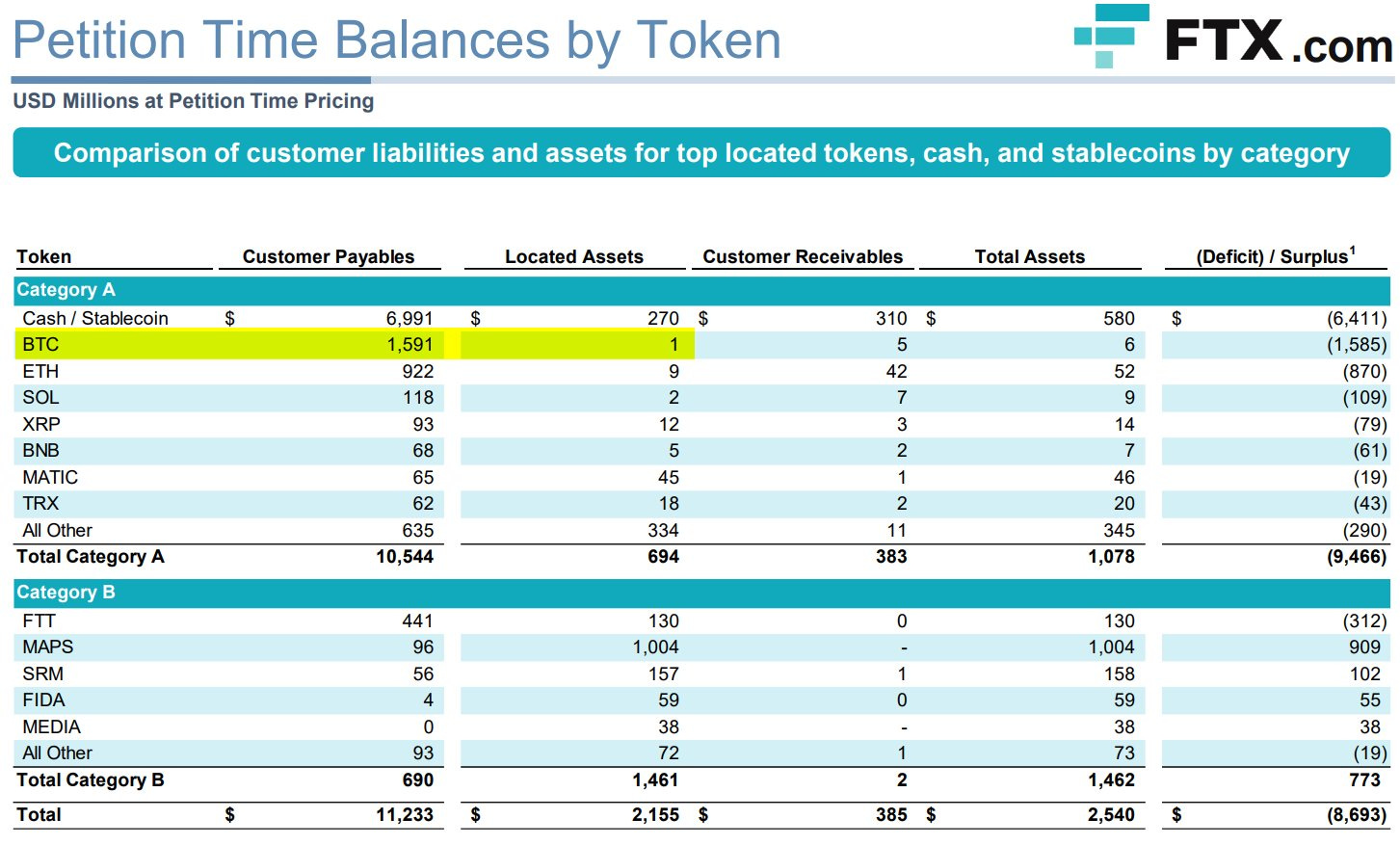
How common are hacks and bugs? Rekt News publishes a leaderboard of significant crypto losses, many are DeFi protocols.
Even if there is no malicious activity, a poorly designed smart contract could fail to return investor funds due to a software bug. An example would be when the contract is expecting to have a certain balance of Ether, but somebody accidentally sends Ether to the contract address. If the code isn’t designed to handle this case, funds could be permanently lost.
Notice how many of the losses are classified as “unaudited”.
It is essential for DeFi protocols and applications to undergo rigorous security audits by reputable independent third-party auditing firms. These audits are designed to expose bugs in the code, vulnerabilities which could be exploited by attackers (including economic exploits), but they also shed light on the skill and professionalism of the protocol’s software developers.
Key takeaway: being audited doesn’t prevent a protocol being hacked, but audits are an essential step in the security process - avoid unaudited protocols and those with poor reports
For our paid subscribers, we deep dive into smart contract audits to help you identify the safe DeFi protocols and minimize risk. It’s essential to learn this because rewards are made by being an early DeFi adopter. By the time a protocol is regarded as generally safe to use, most of the investment gains have been realized.
The Lindy Effect
The Lindy Effect suggests that protocols and projects that have been around for a longer time are more likely to avoid failure than newer ones. “Lindy” protocols have had time to undergo scrutiny and testing.
Beware when DeFi apps drift from their Lindy state. This could involve feature creep, new integrations, allowing poor quality collateral which endangers the solvency of a whole lending protocol, or investing an increasing proportion of assets in blacklistable, centralized, or even off-chain assets.
Here’s just one example.
The original and therefore most Lindy stablecoin (Collateralized Debt Position) protocol is Maker DAO, covered here (Part 1, Part 2, Update). However as you’ll see in our update, Maker has reached a scale where it faces new challenges and may no longer be as safe to use. Credible alternatives include Liquity’s LUSD (Deep Dive).
Tips For Improving Your Security
Use A Hardware Wallet
This is the quickest and cheapest way to boost security
Get A Dedicated Computer For Crypto
If you’re doing DeFi on the same computer you use to browse the web and open email attachments, it’s only a matter of time before malware tricks you into signing a malicious transaction. We’ve seen code which replaces Ethereum addresses in the copy and paste clipboard, and there’s sophisticated targeted malware like the one which even fooled a smart DeFi founder (Hugh Karp).
Mobile Hot Wallets? If you use, only deposit what you can afford to lose
For various reasons it’s quite hard to secure a mobile phone. A good way to think about security here is to only store an amount you’d be comfortable carrying as cash in your physical wallet.
Have A Cold Wallet (Vault), Never Access It
The majority of your crypto savings should be in an account you never access, with the keys (hardware wallet, cryptosteel, or multisigs of these) stored safely away. If you need to withdraw, do a basic ETH or token transfer to another address you control. Keep valuable NFTs in this wallet too. Never “connect” it to a website or sign any messages.
Learn How Transactions Work
Steps 1-4 get your security to the point where you’re likely to lose from your own errors (social engineering, fake transactions) rather than a direct theft of your keys or hacking your device. There are many good scams which can trick you. Did you know it’s possible to lose all the USDC in your wallet just by signing a message? Learn about gasless signatures, token approvals (and how to revoke them in an emergency). We’ve more content on this here (for paid subs)
Use A VPN
Better for you if the cafe/hotel you’re sitting in doesn’t know you’re logged into something crypto. Better if the ad networks don’t know. Better if Google doesn’t know, since it already knows far too much about you. Eventually all this information will leak and make some crypto users a target for crime. Using a VPN will also prevent another user on the free WiFi network redirecting you to a malicious site instead of the DeFi app you wanted.
Trust Lindy Protocols, but…
…keep up with protocol governance to be alert for any major changes. DeFi Ed can save you time here.
Avoid Holding Centralized Stablecoins
Circle’s USDC, Tether’s USDT, and Paxos/Binance’s BUSD all have “blacklist” functions in their smart contracts. Toggling this makes funds non-transferable.
This post scratches the surface of what there is to learn about crypto security. To access our deep dives on the major DeFi protocols, including our opinions on security, become a subscriber today.
Disclaimer: None of this is to be deemed legal or financial advice of any kind. These are opinions from an anonymous group of cartoon animals with Wall Street and Software backgrounds.
We now have a full course on crypto that will get you up to speed (Click Here)
Security: Our official views on how to store Crypto correctly (Click Here)


Hello DeFi team,
Have you looked into the Bit Box wallet and app, https://shiftcrypto.ch or the Coldcard wallet?
Any updates on the computer offering you are planning to launch?
Any chance you would do an open Q/A on VPN and Security in the near future?