Quantum AI Bitcoin
Level 3 - Virgin DeFi Analyst
Welcome Avatar!
Quantum computing and quantum cryptography have been in the news recently.
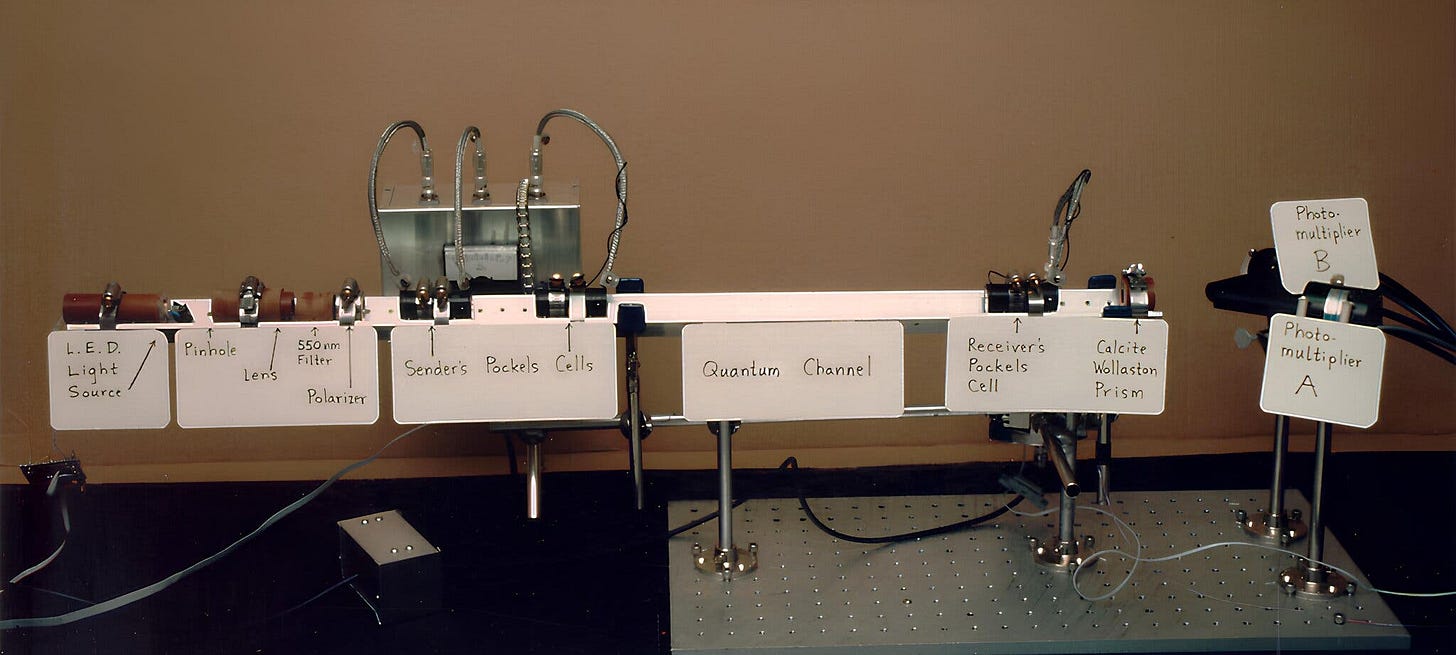
In the 1980s, Charles Bennett and Gilles Brassard created quantum encryption and have recently been honored with a Turing Award (Nobel Prize of computer science). The lore runs that while swimming off the shore of Degen Island Puerto Rico “Dr. Bennett swam up to Dr. Brassard and suggested they use quantum mechanics to create a bank note that could never be forged.” Forty years later, it is poised to become an essential way of protecting the world’s most sensitive information.
If you’ve heard of quantum in a cryptocurrencies context, you’re probably aware that there’s some risk of advances in this field breaking some key security protections we rely on in public blockchains.
Today, Google Quantum AI published a whitepaper on The Cost of Breaking Cryptocurrencies. Bears have recently been shouting (again) about quantum computing being the driver of BTC’s recent price performance. We’ll break down what’s happening so you can come to your own conclusions.
What Is Crypto Anyway?
Cryptography relies on a mathematical asymmetry: some operations are simply harder to perform than others - or stated another way, some things are easier to “do” than “un-do”. It’s easier to smash an egg than reassemble the result. Similarly it’s easier to multiply two prime numbers than it is to find the prime factors of a large number.
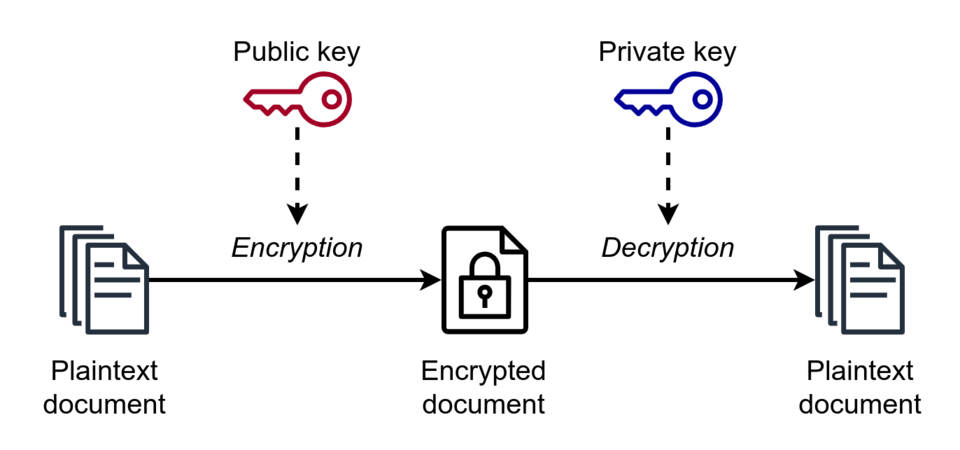
To encrypt a message we combine the plaintext with a key to create ciphertext. Without the key, reversing this process is exponentially more computationally intensive. You can encrypt all the personal data you own with the processing power of a cell phone, but the combined power of all the computers in the world running until the world runs out of energy couldn’t decrypt it by brute force.
As processing power increased exponentially according to Moore’s Law, it’s true that some early encryption algorithms with relatively short key sizes became breakable due to faster technology. But adding just 1 bit to the key length doubles the computational cost to break. Therefore the obsolete DES (56 bit) was replaced with Triple-DES (168 bit), 128 bit symmetric ciphers, and eventually the 256 bit cryptography which secures the Internet (and Bitcoin) today. If 256 bit keys were under threat from current computer power, we could simply adopt 512 bit keys. Doubling the key length would double the cost to break 256 times. That’s a number too long to write here.
That’s the simple overview, but the asymmetric property discussed earlier is based on our knowledge of math. Cryptographers extend mathematical knowledge all the time, and some of their discoveries mean that it’s easier to reverse the encryption process. This is a good reason to use key lengths longer than we think necessary. It provides some overhead if, suddenly, a genius discovers a 25% more efficient way to brute force.
This has been known for a long time. For example, the quantum search algorithm devised by Lov Grover in 1996 speeds up brute force attacks on symmetric encryption using quantum computing, essentially halving the key length. Shor’s algorithm (1994) is a stronger attack on public key cryptography (websites and crypto), where doubling the key length yields only an 8-fold increase in computing power required to break. If quantum computing ever scales like Moore’s Law this puts current crypto security in jeopardy. This is a theoretical attack: it took from the year 2001 to the year 2012 to grow the size of the number being factored from 15 (5x3) to 21 (7x3).
Yes, similar to how cutting-edge and over-hyped “AI” can’t solve a theme park video game for 12 year olds, the much feared “quantum computing” can’t factor anything larger than two digit semi-primes within the grasp of a grade-school math student.
So is this a real threat which merits the attention given by Google, government agencies, and crypto bears - or just another poorly understood tech where the hype/FUD doesn’t match reality? Let’s dive in!
How Could “Quantum” Affect Our Crypto?
Encryption schemes can be lumped into two groups - symmetric cryptography and public key cryptography. Grover’s algorithm basically limits the entire effect of quantum computing to halving the key length. In other words if we upgraded every 256 bit symmetric key to 512 bits that would cancel out quantum breakthroughs. Symmetric cryptography as the name suggests requires that an encrypter/signer and decrypter/verifier must possess the secret key. Public blockchains are unworkable with this type of encryption - the key needed to validate that a transaction is correctly authorized would be the same key which could spend all funds from the account.
Public blockchains secured by crypto rely on public key cryptography, which as the name suggests allows publishing the public part of the key while only the account owner retains and uses the private key. Public key cryptography also secures the web. And it is public key cryptography which is deeply vulnerable to quantum computing.
Now you may have read the argument that if Bitcoin crypto security is broken by quantum, all other (public key) cryptography is also broken and we’d have bigger problems. However symmetric cryptography (not broken by quantum) could replace public key crypto - GSM, the cell phone standard; and Kerberos, the ticket based network authentication protocol from the 1980s - both ran on symmetric crypto. Public blockchains would be uniquely affected with no plausible replacement beyond hash based signatures (which are already being considered in post-quantum blockchain research).
Benefits of Quantum Computing
This is a tl;dr of what published experts have declared is possible, in theory, if the machines can be built and scaled up. We’re not quantum scientists:
drug discovery, molecular simulations: e.g. protein folding at a rate not possible even with massive distributed computing projects like Folding@Home
materials science: quantum simulation of atomic level interactions to design new chemicals
Risks of Quantum - Harvest Now, Decrypt Later
Nation state level actors (and even some sophisticated organized crime groups) have the technical ability to intercept and store encrypted communications. Once quantum hardware exists: all your financial data, ID documents, private communications, trade secrets, etc are visible.
Implications For Crypto
Signature cryptography attacks: a quantum computer running Shor’s algo (above) could theoretically derive the key (simplistically, the seed phrase) to a wallet just from the unhashed public key (address). Look up the biggest holders on the blockchain, save down their address, and try to crack their seed. Something which is impossible now could be trivial with quantum. The only wallets which are theoretically safe are those which have never spent funds, but an attack could be feasible on networks like Bitcoin with a slow block time.
Broadcast transaction → sits in mempool → attackers compete to crack your key in under 10 mins (BTC block time) and submit a competing transaction stealing funds
The major myth is that quantum can rewrite the blockchain, giving an attacker arbitrary control. This isn’t the case, the SHA256 hash which secures the blockchain by including the hash of the prior block in the current block only faces the upper bound of Grover’s algo - an effective reduction to 128 bit key size, still too large to brute force. All serious papers acknowledge this, including Google’s most recent.
Google’s Paper
Quantum x Bitcoin is back in the news this week due to a paper released by Google.
This paper focuses on attacks against the 256-bit Elliptic Curve Discrete Logarithm using secp256k1, the parameters of the elliptic curve used in Bitcoin and Etherum public-key cryptography. The key takeaway is a roughly 10x improvement in the computing resources needed to mount a successful attack, bringing the timeline forward.
Interestingly, claims are validated through zero-knowledge proofs. We think this is the first published example in all of information security of a public disclosure proving a threat but without revealing any details which could be used by an attacker. This is probably worthy of an entire article on how this evolves the concept of responsible disclosure, but…back to crypto.
Types of Attack:
“On spend” attacks - the attacker sources a public key from a pending transaction in the mempool and attempts to derive the private key before the transaction is included in the block. If successful, he bribes a miner to have his forged transaction included in the next block, stealing all the money. This approach requires being able to break the key within the block time - feasible for Bitcoin (~10 minutes), far less likely for Ethereum (~10 seconds).
“At rest” attacks. Any public key which has been spent from. Dormant wallets or reused addresses. Will likely target dormant wallets where the operator has lost the keys and can’t upgrade/avoid by moving funds to a fresh wallet.
“On setup” attacks. An attacker could wait for a DeFi protocol to deploy its new smart contracts and crack the admin key. Or other quantum-based recovery / attack approaches to derive secret key material from key ceremonies.
Types of Architecture:
“Fast clock” quantum could solve elliptic curve based public key cryptography in minutes. Fast enough to break all exposed Bitcoin addresses and allow on-spend attacks. If this architecture can be built it’s the worst case scenario for crypto.
“Slow clock” quantum makes only “at rest” attacks viable. Meanwhile, the industry likely mitigates public key exposure (auto sweep existing balances to new undisclosed wallets using new software frontends and hw wallet upgrades). This means active crypto users protect their funds but would still bring previously dormant supply online, which could be consequential given the percentage of supply which we consider likely permanently lost/burned by early whale key loss.
Early Bitcoin transactions (P2PK - Pay to Public Key), ~10% of supply, including Satoshi era wallets, are exposed. Vulnerable to on-spend and at rest attacks.
Pay to Public Key Hash (P2PKH) are immune to at-rest attacks because of the hash.
Pay to Taproot addresses (P2TR), introduced by the Taproot “upgrade”, is arguably a security regression because the absence of a hash results in the publication of the full public key on chain, which is the input needed to derive the private key in a quantum brute force context. Worryingly a large share of Bitcoin is stored in these addresses. Bitcoin mitigates this with Pay to Merkle Root (BIP 360) - if adopted we go back to pre-Taproot security - dormant wallets are immune, but there’s still a race condition for on-spend attacks.
Ethereum Risks
The account vulnerability is worse in Ethereum: as you all know, whenever an EOA sends a transaction it exposes the public key permanently. There is no possibility of key rotation - the wallet address is the unique identifier.
Smart contracts with admin keys are an obvious attack vector. Any smart contract with ownership rights can have its admin address public key compromised. Read that again and think of the permissioned mint function on stablecoins. Then bridges, oracle nodes…would be a disaster for DeFi.
Ethereum also hosts immutable software code (smart contracts) which cannot be automatically upgraded to become quantum-secure even if the base layer upgrades.
And at the consensus layer, Ethereum’s Proof of Stake uses an elliptic curve. Cracking validator private keys allows the attacker to make the nodes misbehave: equivocating (and being slashed/ejected). To mount an attack on the whole network at least 1/3rd of stake would need to be compromised (liveness failure), which seems unlikely. A 2/3rds majority could allow reorgs, censorship, basically game over for Ethereum unless a social consensus fork allows the network to recover.
Finally the data availability layer could also be attacked, allowing an attacker to forge DA proofs. On the surface Ethereum looks far more exposed to quantum attacks than Bitcoin (as a consequence of Ethereum having more functionality beyond send payments).
There are two important mitigants:
fast block times make on-spend attacks impractical
there’s a Foundation in charge of coordinating updates and a staking community with a … pardon … stake in ensuring that Proof of Stake isn’t compromised
In contrast we’d be expecting the three branches of Bitcoin government to actually function to upgrade the network, which seems less realistic than Vitamin Butane, Lido, and Blackrock Staked ETH ETF getting behind a solution.
Key Ceremonies
This is more of an autist note but the ability to recover cryptographic secrets from the initial setup phase -the key ceremony- means that a protocol could become permanently cracked with even non-quantum attackers able to exploit access once the secrets are known. This mainly impacts zero knowledge protocols, but Ethereum Data Availability is also a vulnerable target:
Many commitment schemes and ZK protocols rely on the assumption that nobody knows certain secrets related to the protocol’s fixed public parameters. For some schemes, such as the KZG polynomial commitments, the secrets, sometimes referred to in this context as “toxic waste”, are known temporarily before being erased during the trusted setup ceremony in the course of which the protocol parameters are first established. For other schemes the parameters are produced by methods satisfying the Nothing Up My Sleeve (NUMS) principle to ensure that nobody learns them in the process of choosing protocol parameters. However, for certain ECDLP-based protocols the secrets can be derived from the fixed public parameters using a [quantum computer]. Moreover, since protocol parameters are fixed, this needs to be done only once and the resulting secrets can be reused to launch multiple attacks later using classical computers. Example protocols vulnerable to such on-setup attacks include Pedersen commitments used in Mimblewimble, KZG commitments used in Ethereum’s Data Availability Sampling mechanism, and BulletProofs used in Monero and Mimblewimble.
Google’s conclusions are that it takes fewer quantum computing resources to break cryptocurrencies than previously estimated, roughly by a factor of 10. This brings the timeline forward and the community should prioritize work on post-quantum security upgrades. Google are not saying that the problem is intractable and that Bitcoin will go to zero, or even that quantum computing will ever reach the scale where it can reliably work on large numbers. The authors explicitly state that the margin for delay is narrowing and urge immediate action. They’ve got the attention of the major players and post-quantum security is now on everyone’s agenda.
Mitigation approaches involve whitehack recoveries of dormant wallet assets authorized by the state and carried out by industry before these assets are accessed by hackers. Recoveries can either be returned to their rightful owners upon a show of proof forfeited to the state (inflationary), or even burned (preserving the status quo ante quantum).
The paper deliberately avoids predicting when viable quantum computers will exist!
Concluding Thoughts
The bottom line is that around 1/3rd of BTC supply is estimated to be vulnerable to at rest style quantum attacks. Around 10% of the BTC supply is estimated to be dormant. Releasing that BTC into circulation essentially dilutes others, but active users who stay informed and co-operate with any upgrade procedures are unlikely to lose BTC. The second order effects described in the paper are concerning for the valuations of most of the large cap cryptoassets.
It’s worth recapping the higher impact effects:
fiat backed stablecoins rely on centralized admin keys controlling the mint function: if compromised, the attacker can literally print unbacked USDT/USDC - with more than a quarter trillion dollars in stablecoins this creates a “too big to fail” issue which should draw attention from regulators
much of DeFi relies on either unupgradable smart contract code or code controlled by admin keys - quantum would be catastrophic for DeFi
on-setup attacks are probably the most serious vector: entire protocols can be irreversibly compromised and the exploit sold on the black market to non-quantum-capable actors
How do we rank the threat? Somewhere between “Crypto’s Y2K moment” and Scott Adams’ Law of Slow-Moving Disasters. In other words any serious danger we see coming far in the future we always find a way to fix. Adams cited examples of previous predictions of running out of food or oil: “we have an unbroken track record of avoiding doom”.
We’d rank technology developments which threaten the cryptographic systems which underpin nearly all commerce as a slow moving disaster that government and industry will necessarily mitigate before it becomes a threat. Quantum is an easy ex-post-hoc rationalization for why we are in a crypto bear market.
The bottom line is that no quantum computer has ever broken a cryptographically relevant problem, the track record consists of some combination of sleight of hand and magic tricks factoring toy numbers, and the burden of proof remains firmly on those asserting there’s an imminent threat from a magical technology with the power to invent miracle drugs and destabilize society (AI anyone?). For anyone with the math chops to go deeper, this paper from 2025 sums it up.
Paid subscribers also get access to:
All of our past posts
Weekly Deep Dive Report
A comprehensive bi-weekly DeFi Roundup
Bi-weekly Q&A sessions with our team
Until next time..
Disclaimer: None of this is to be deemed legal or financial advice of any kind. These are opinions from an anonymous group of cartoon animals with Wall Street and Software backgrounds.
We now have a full course on crypto that will get you up to speed (Click Here)
We offer the Prediction Markets module on a standalone basis (Click Here)
Security: Our official views on how to store Crypto correctly (Click Here)

Thanks for the wonderful write-up. I have been waiting for this since Google published its paper yesterday.
I just checked that all my web browsers are post-quantum safe. It looks like the world is already prepared for quantum computers, and we should not be alarmed when commercial-grade quantum computers are ready for full deployments in the next few years.
The real problems for BTC are those older wallets. Will the community move these wallets to a post-quantum side-chain bitcoin network, or will the authorities already be trying to seize them? You know what I mean, right?
Actually, I do know of a new type of problem on the horizon that probably most people may not be aware of, and that is the roll-over date-time problem on all 32-bit computing systems, and that happens precisely upon the turn into the year 2035. It is clear that these legacy systems will create another problem, similar to the Y2K problems/scares that we had before. The cryptographic key exchange mechanism will fail on timestamps that will roll over to the year 1970 for older Linux/Windows systems.
Send in the Saylor